CCNA and CCENT Tutorial: Wildcard Masking Made Easy
In the first installment of this ACL tutorial series, we took a look at some basic ACL lines. It became apparent very quickly that we need to have wildcard masking down cold, since they’re used in many lines of an ACL (not to mention OSPF and EIGRP configs).
Wildcard masks look like network masks or subnet masks, but they really mirror those mask types. When used with ACLs, wildcard masks use zeros and ones this way:
- Zeros are “I care” bits, bits that must match in order for this ACL line to take effect.
- Ones are “I don’t care” bits, bits that don’t have to match at all for the ACL line to be considered a match.
This all becomes much clearer with an example, so let’s dig into one. We need an ACL that allows packets sourced from 196.17.100.0 /24 to enter the router’s FastEthernet interface, and packets sourced from all other addresses should be prohibited.
To make this happen, we need an ACL that allows packets to enter if the source IP address matches the first three octets exactly (196.17.100), and after that, we don’t care.
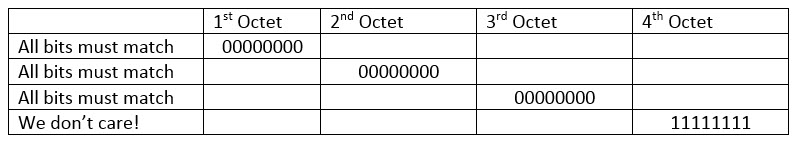
Converting that string to dotted decimal, the resulting wildcard mask is 0.0.0.255. It looks odd at first, but you’ll get used to it quickly. Watch these masks on the exam. Don’t select a mask of 255.0.0.0 for an ACL when you need a wildcard mask of 0.0.0.255.
In the previous section, I mentioned that ACLs aren’t just for blocking and permitting traffic. They’re also used to identify traffic as well as for EIGRP and OSPF configs. Let’s take a look at how they’re used in OSPF. (If you haven’t gotten to OSPF yet in your studies, that’s fine.)
In this lab, the Serial interface’s IP address is 172.12.12.12 /28 and the Fast Ethernet interface’s address is 172.12.12.17 /28.
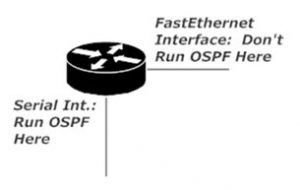
The Serial interface is on the 172.12.12.0 /28 subnet, while the FE interface is on 172.12.12.16 /28. We want to run OSPF on the Serial interface, but not the FE interface. Wildcard masks make this possible. We just need to determine the wildcard mask that matches 172.12.12.0 /28.
To determine the wildcard mask in seconds, just invert the subnet mask, and that gives you the wildcard mask. The subnet mask on the interfaces was /28, or 1111111 11111111 11111111 11110000. Just change those zeroes to ones and ones to zeroes, and you have 00000000 00000000 00000000 00001111, your wildcard mask. When you’re comfortable with binary, you can do that one in your head — with practice!
Time to take a look at the standard ACL, followed by some lab work that just might give us more wildcard masking practice. Let’s head on over!
Chris B.